8.8.2 Quiz Module 8 Troubleshooting Common Security Issues Answers
8.8.2 Quiz Module 8 Troubleshooting Common Security Issues Answers
The 8.8.2 Quiz Module 8 Troubleshooting Common Security Issues Answers is designed to help learners assess their understanding of identifying, analyzing, and resolving common network security problems. This module focuses on key troubleshooting techniques related to security configurations, including firewall rules, access control lists (ACLs), authentication issues, and endpoint protection. By reviewing these quiz questions and answers, students can strengthen their ability to diagnose security vulnerabilities, apply appropriate mitigation strategies, and maintain a secure and resilient network environment.
1. How have cyber threats evolved from the 1970s to the present day?
- Early malware was limited in impact, but the rise of the Internet and modern technologies has enabled global, sophisticated cyberattacks.
- Cyber threats have remained mostly experimental and are rarely seen outside research environments.
- Attack methods have changed little over the years, with viruses continuing to be the primary daily threat across most systems globally.
- The main concern in cybersecurity remains preventing the accidental download of harmful files while using work tablets and desktops at the workplace.
With the expansion of the Internet in the 1990s, cyber threats became a global issue. File-sharing services contributed to malware dissemination, and new threats like ransomware, AI-driven attacks, and persistent threats now dominate. Attackers exploit cloud services, legacy systems, and smart devices, using tactics that are far more sophisticated than those of the early digital era.
2. A hacker has identified several active IP addresses on a target network using a ping sweep. The hacker then uses a tool to check which applications are open on these active IP addresses and identify available services. Which reconnaissance technique is the hacker using at this point?
- ping sweep
- information query
- port scan
- vulnerability scan
A port scan is used to detect which ports are open and which services are running on the target system. Tools like Nmap or Angry IP Scanner are commonly used for this purpose.
3. Match each type of virus to its description.
- Firmware Virus ==> Infects the underlying software embedded in hardware components, potentially affecting how the device operates even before the OS loads.
- Macro Virus ==> Exploits built-in scripting features in productivity software to run harmful commands when documents are opened.
- Boot Sector Virus ==> Targets the code that loads before the operating system, often compromising system startup and file access.
- Program Virus ==> Attaches itself to legitimate software files, activating when the compromised application is launched.
4. After clicking a suspicious link, a user’s antivirus software and firewall are mysteriously not working. The user reports that they did not alter any settings. Which type of Trojan horse likely caused this issue?
- Denial of Service
- Keylogger
- Data-sending
- Security software disabler
The security software disabler type of Trojan is specifically built to disable or bypass antivirus and firewall protections, allowing other malware to act undetected on the system.
5. A group of activists launches a cyber attack against a government agency to protest new legislation. What classification would best describe these individuals?
- Cyber Criminals
- Hacktivists
- Terrorist Group
- Corporate and Industrial Spies
These individuals are Hacktivists, as they engage in cyber attacks to advance a political cause or ideology, using their skills to protest against entities they oppose.
6. What is the primary purpose of an Incident Response Plan as defined by the U.S. National Institute of Standards and Technology (NIST)?
- to provide training to improve response time issues for software development teams
- to increase the speed of internet connections
- to enhance user interface designs for software applications
- to limit the impact of a cyberattack and implement recovery procedures
The primary purpose of an Incident Response Plan is to limit the impact of a cyberattack by assessing the damage and implementing recovery procedures. By following established guidelines such as NIST SP 800-61, organizations can effectively manage and respond to security incidents.
7. Which action could potentially be taken by an internal user (such as an employee) that poses a serious risk to a company’s network security?
- Forget to review company policies on proper data usage.
- Disconnect a critical network connection and cause a network outage.
- Send an inappropriate email to a colleague.
- Regularly update passwords for personal accounts while at the workplace.
An internal user has the potential to disrupt critical operations by disconnecting network connections. This can lead to significant downtime and impact various services. Internal users often have access that could allow for actions that result in severe consequences for the organization.
8. Match the data loss vector with its corresponding description.
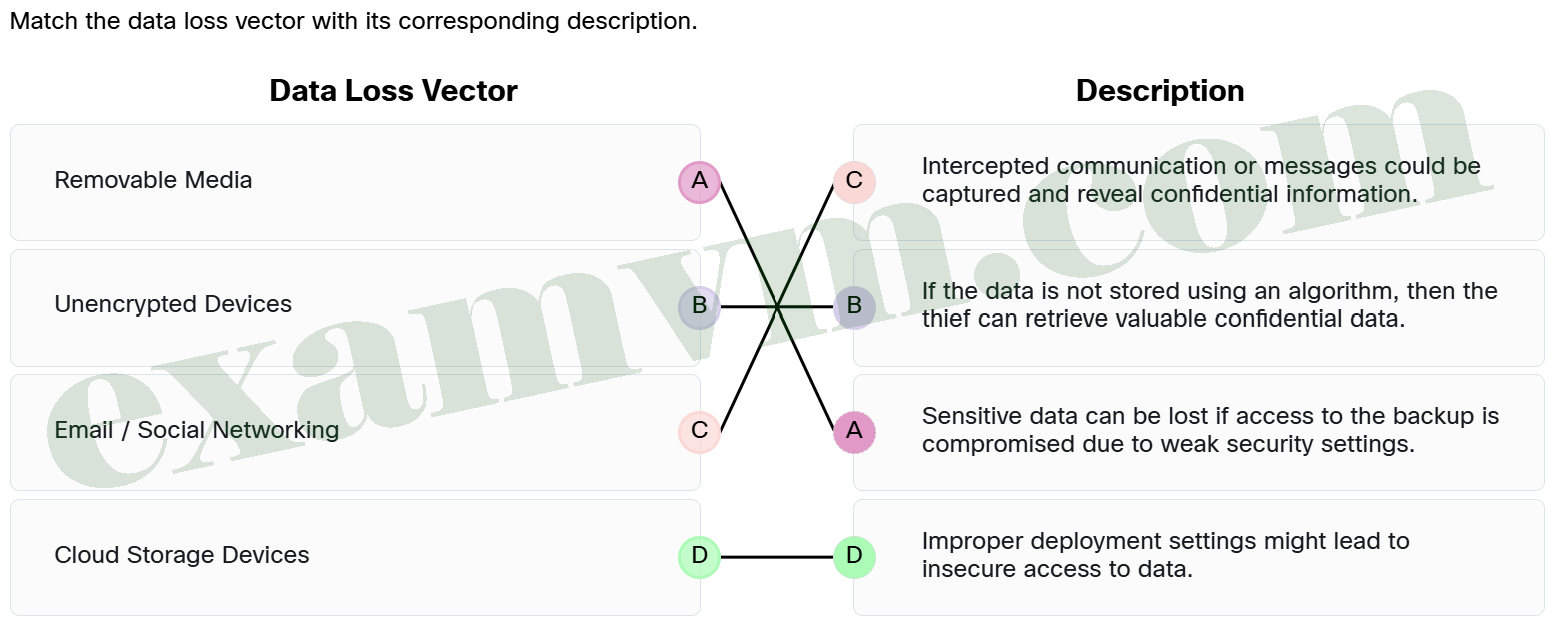
- Email / Social Networking ==> Intercepted communication or messages could be captured and reveal confidential information.
- Cloud Storage Devices ==> Improper deployment settings might lead to insecure access to data.
- Removable Media ==> Sensitive data can be lost if access to the backup is compromised due to weak security settings.
- Unencrypted Devices ==> If the data is not stored using an algorithm, then the thief can retrieve valuable confidential data.
Intercepted emails or IMs can expose sensitive information, making a significant data loss vector. If devices lack encryption, sensitive data on them is vulnerable to theft. Weak security settings can lead to unauthorized access, risking data stored in the cloud. Additionally, it is important to manage removable media wisely because it poses risks of unauthorized data transfer and loss.
9. A teenager uses available hacking tools to disrupt the online services of a school as a prank. What type of hacker is this individual most likely to be?
- Hacktivist
- Vulnerability Broker
- Cyber Criminal
- Script Kiddie
This teenager fits the definition of a Script Kiddie, as they are inexperienced hackers utilizing existing tools to cause disruption, often without malicious profit motives.
10. Why is it important for users to understand malware and its impact on end devices?
- Malware rarely causes real harm and only temporarily affects device speed.
- Malware affects outdated software and is a major concern for modern systems.
- Most end devices are now automatically protected by antivirus software and do not require further user caution.
- Threat actors depend on users to unknowingly install malware, making user awareness a key defense.
Malware is often installed through user interaction – clicking on malicious links, opening infected attachments, or downloading suspicious software. Since end devices like laptops and smartphones are common targets, educating users is essential. Awareness helps prevent threat actors from exploiting human behavior to bypass technical defenses and gain access to systems.
11. A cybersecurity team at a large financial institution discovers unusual traffic patterns on their network. Upon investigation, they find that an IP address has been used in scanning their system for open ports and services, potentially looking for weaknesses. What type of attack is observed and what is its primary purpose?
- Phishing Attack – to steal user credentials through deceptive emails.
- Reconnaissance Attack – to gather information about the network’s vulnerabilities.
- Malware Delivery – to infect systems with malicious software.
- Denial of Service Attack – to overwhelm the network and render it unusable.
A reconnaissance attack is focused on gathering information about a network’s vulnerabilities, much like a thief scouting potential targets. This initial phase is crucial for attackers as it helps them plan their next move, whether it’s attempting unauthorized access or launching a more disruptive attack. Understanding this behavior can help organizations strengthen their security measures.
12. A company’s security team notices that an attacker is using a list of common passwords, such as “password123,” “admin123,” and “letmein,” in an attempt to gain unauthorized access to employee accounts. The attacker is trying these passwords across multiple user accounts. What type of password attack is most likely being used?
- password spraying attack
- credential stuffing
- dictionary attack
- rainbow table attack
A dictionary attack uses a list of common passwords (often taken from word lists or common phrases) to try and guess a password. This scenario describes an attacker using a set of commonly used passwords, which is typical of a dictionary attack.
13. What is a key benefit of using a host-based security suite on both home and business networks?
- It provides a layered defense against common threats.
- It ensures that all software is automatically updated.
- It increases the download speed of files and scans them for all possible threats.
- It eliminates the need for any additional security measures.
Host-based security suites, which include features like antivirus, anti-phishing, and firewalls, offer a comprehensive defense mechanism that helps protect against various threats, necessary for maintaining security in both home and business environments.
14. What should a user do if the antivirus scan fails to remove a persistent malware infection from the computer?
- Perform a quick scan and then continue usage.
- Restart the computer and then continue usage.
- Ignore the infection and continue using the computer as normal if no pop-ups are seen.
- Update the antivirus software to ensure it has the latest malware definitions.
Updating the antivirus software is important when dealing with persistent malware infections. This ensures that the antivirus has the latest definitions to detect and remove newer threats that may not have been previously identified.
15. A company’s security team uses the Social Engineering Toolkit to conduct a test on their employees. The goal is to simulate an attack that attempts to manipulate employees into revealing sensitive information or performing actions that could compromise the network. As part of the test, the security team designs a scenario where an attacker impersonates an executive and asks an employee for confidential data over the phone. Why is it important for the company to educate its employees about social engineering risks and develop strategies for identity validation?
- to help employees recognize signs of network intrusions from malicious software
- to ensure employees can identify phishing emails and phone calls more easily
- to make sure employees understand how to prevent viruses from spreading through the network and train them on proper security protocols
- to prevent unauthorized access by attackers who use deception to manipulate employees into disclosing sensitive information
Educating employees about social engineering helps prevent attackers from using deceptive tactics to manipulate individuals into disclosing sensitive information, which can lead to unauthorized access and security breaches.
16. During a routine system check, an IT technician notices several unusual pop-ups appearing on a user’s computer screen, which have never been seen before. What should be the first step taken to investigate this potential security incident?
- Observe and recognize the unusual system behavior.
- Interview the user to determine recent activity.
- Compile a comprehensive report for higher-level IT security teams.
- Collect logs from various systems to analyze patterns.
The first step in investigating a potential security incident is symptom identification, which involves closely observing and recognizing any signs of abnormal behavior on the system. This step is crucial for accurately assessing any potential security breaches before further actions are taken.
17. A cyber criminal calls a company’s help desk, posing as an employee who is locked out of their account. The attacker claims they urgently need access to a sensitive system and pressures the help desk staff to reset their password and unlock the account. The help desk staff, trusting the urgency of the situation, grants the request, giving the attacker unauthorized access to critical systems. What type of attack is the cyber criminal using in this scenario?
- social engineering attack
- password spraying attack
- brute-force attack
- man-in-the-middle attack
This is a social engineering attack, where the attacker manipulates the help desk staff by exploiting trust and urgency. The attacker uses psychological tactics to gain unauthorized access to sensitive systems.
18. Match the guidelines for defending against social engineering threats to the description.
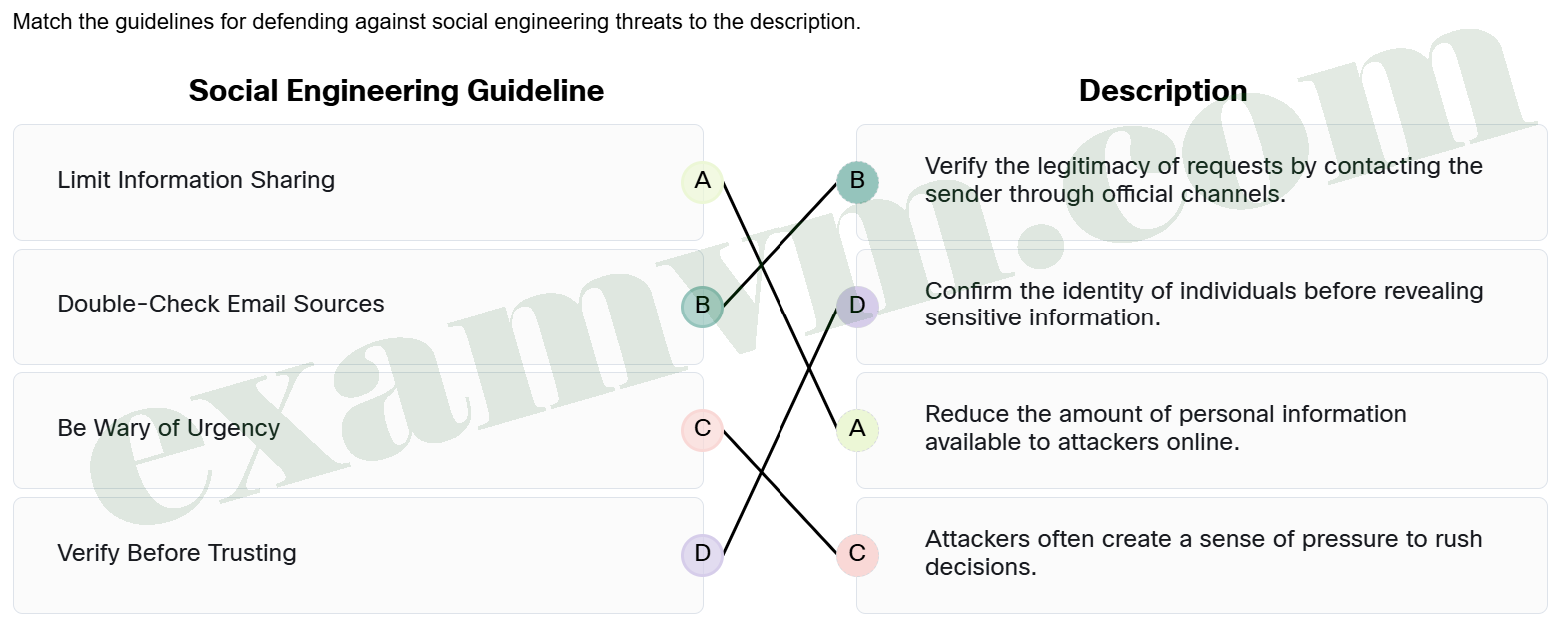
- Limit Information Sharing ==> Reduce the amount of personal information available to attackers online.
- Double-Check Email Sources ==> Verify the legitimacy of requests by contacting the sender through official channels.
- Be Wary of Urgency ==> Attackers often create a sense of pressure to rush decisions.
- Verify Before Trusting ==> Confirm the identity of individuals before revealing sensitive information.